Windows Network Access Suspicious desktop.ini Action
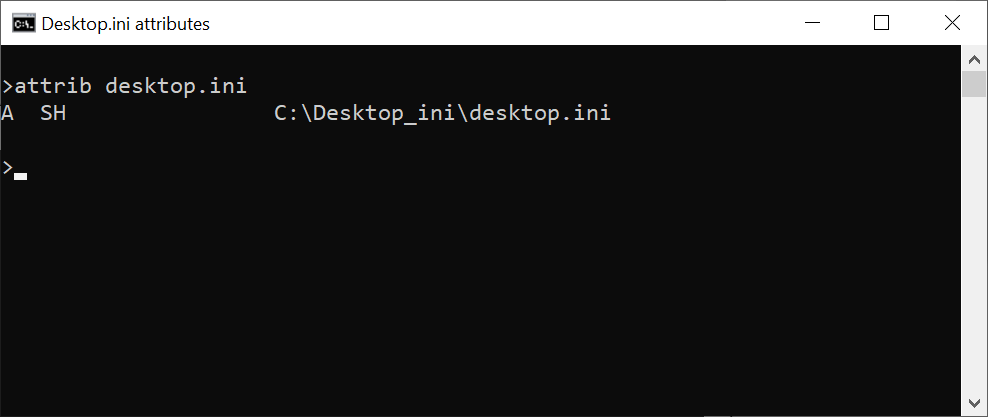
Detects unusual processes accessing desktop.ini remotely over network share, which can be leveraged to alter how Explorer displays a folder's content (i.e. renaming files) without changing them on disk.
Sigma rule (View on GitHub)
1title: Windows Network Access Suspicious desktop.ini Action
2id: 35bc7e28-ee6b-492f-ab04-da58fcf6402e
3status: test
4description: Detects unusual processes accessing desktop.ini remotely over network share, which can be leveraged to alter how Explorer displays a folder's content (i.e. renaming files) without changing them on disk.
5references:
6 - https://isc.sans.edu/forums/diary/Desktopini+as+a+postexploitation+tool/25912/
7author: Tim Shelton (HAWK.IO)
8date: 2021-12-06
9modified: 2022-01-16
10tags:
11 - attack.privilege-escalation
12 - attack.persistence
13 - attack.t1547.009
14logsource:
15 product: windows
16 service: security
17detection:
18 selection:
19 EventID: 5145
20 ObjectType: File
21 RelativeTargetName|endswith: '\desktop.ini'
22 AccessList|contains:
23 - 'WriteData'
24 - 'DELETE'
25 - 'WriteDAC'
26 - 'AppendData'
27 - 'AddSubdirectory'
28 condition: selection
29falsepositives:
30 - Read only access list authority
31level: medium
References
Related rules
- Creation Exe for Service with Unquoted Path
- A Member Was Added to a Security-Enabled Global Group
- A Member Was Removed From a Security-Enabled Global Group
- A New Trust Was Created To A Domain
- A Security-Enabled Global Group Was Deleted