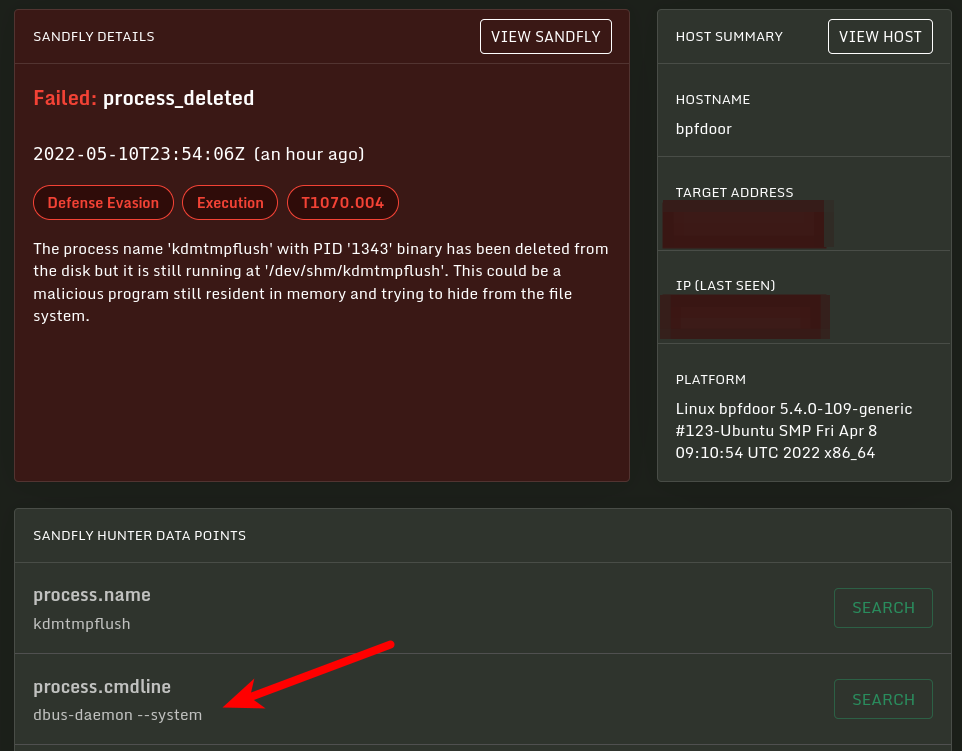
BPFDoor Abnormal Process ID or Lock File Accessed
detects BPFDoor .lock and .pid files access in temporary file storage facility
Sigma rule (View on GitHub)
1title: BPFDoor Abnormal Process ID or Lock File Accessed
2id: 808146b2-9332-4d78-9416-d7e47012d83d
3status: test
4description: detects BPFDoor .lock and .pid files access in temporary file storage facility
5references:
6 - https://www.sandflysecurity.com/blog/bpfdoor-an-evasive-linux-backdoor-technical-analysis/
7 - https://www.elastic.co/security-labs/a-peek-behind-the-bpfdoor
8 - https://www.rapid7.com/blog/post/tr-bpfdoor-telecom-networks-sleeper-cells-threat-research-report/
9 - https://github.com/rapid7/Rapid7-Labs/blob/741c7196ec12a0a56b63463d1fd726ff14d3a97a/BPFDoor/rapid7_detect_bpfdoor.sh
10author: Rafal Piasecki
11date: 2022-08-10
12modified: 2026-03-30
13tags:
14 - attack.execution
15 - attack.t1106
16 - attack.t1059
17logsource:
18 product: linux
19 service: auditd
20detection:
21 selection:
22 type: 'PATH'
23 name:
24 - /var/run/aepmonend.pid
25 - /var/run/auditd.lock
26 - /var/run/cma.lock
27 - /var/run/console-kit.pid
28 - /var/run/consolekit.pid
29 - /var/run/daemon.pid
30 - /var/run/hald-addon.pid
31 - /var/run/hald-smartd.pid
32 - /var/run/haldrund.pid
33 - /var/run/hp-health.pid
34 - /var/run/hpasmlit.lock
35 - /var/run/hpasmlited.pid
36 - /var/run/kdevrund.pid
37 - /var/run/lldpad.lock
38 - /var/run/mcelog.pid
39 - /var/run/system.pid
40 - /var/run/uvp-srv.pid
41 - /var/run/vmtoolagt.pid
42 - /var/run/xinetd.lock
43 condition: selection
44falsepositives:
45 - Unlikely
46level: high
References
Related rules
- Shai-Hulud Malware Indicators - Linux
- Shai-Hulud Malware Indicators - Windows
- Suspicious ArcSOC.exe Child Process
- Linux Suspicious Child Process from Node.js - React2Shell
- Windows Suspicious Child Process from Node.js - React2Shell