Malicious DLL Load By Compromised 3CXDesktopApp
Detects DLL load activity of known compromised DLLs used in by the compromised 3CXDesktopApp
Sigma rule (View on GitHub)
1title: Malicious DLL Load By Compromised 3CXDesktopApp
2id: d0b65ad3-e945-435e-a7a9-438e62dd48e9
3related:
4 - id: 3c4b3bbf-36b4-470c-b6cf-f07e8b1c7e26 # Proxy C2
5 type: similar
6 - id: 76bc1601-9546-4b75-9419-06e0e8d10651 # Proxy GH
7 type: similar
8 - id: bd03a0dc-5d93-49eb-b2e8-2dfd268600f8 # DNS C2
9 type: similar
10 - id: 51eecf75-d069-43c7-9ea2-63f75499edd4 # net_connection C2
11 type: similar
12 - id: 93bbde78-dc86-4e73-9ffc-ff8a384ca89c # ProcCreation Exec
13 type: similar
14 - id: 63f3605b-979f-48c2-b7cc-7f90523fed88 # ProcCreation ChildProc
15 type: similar
16 - id: e7581747-1e44-4d4b-85a6-0db0b4a00f2a # ProcCreation Update
17 type: similar
18status: test
19description: Detects DLL load activity of known compromised DLLs used in by the compromised 3CXDesktopApp
20references:
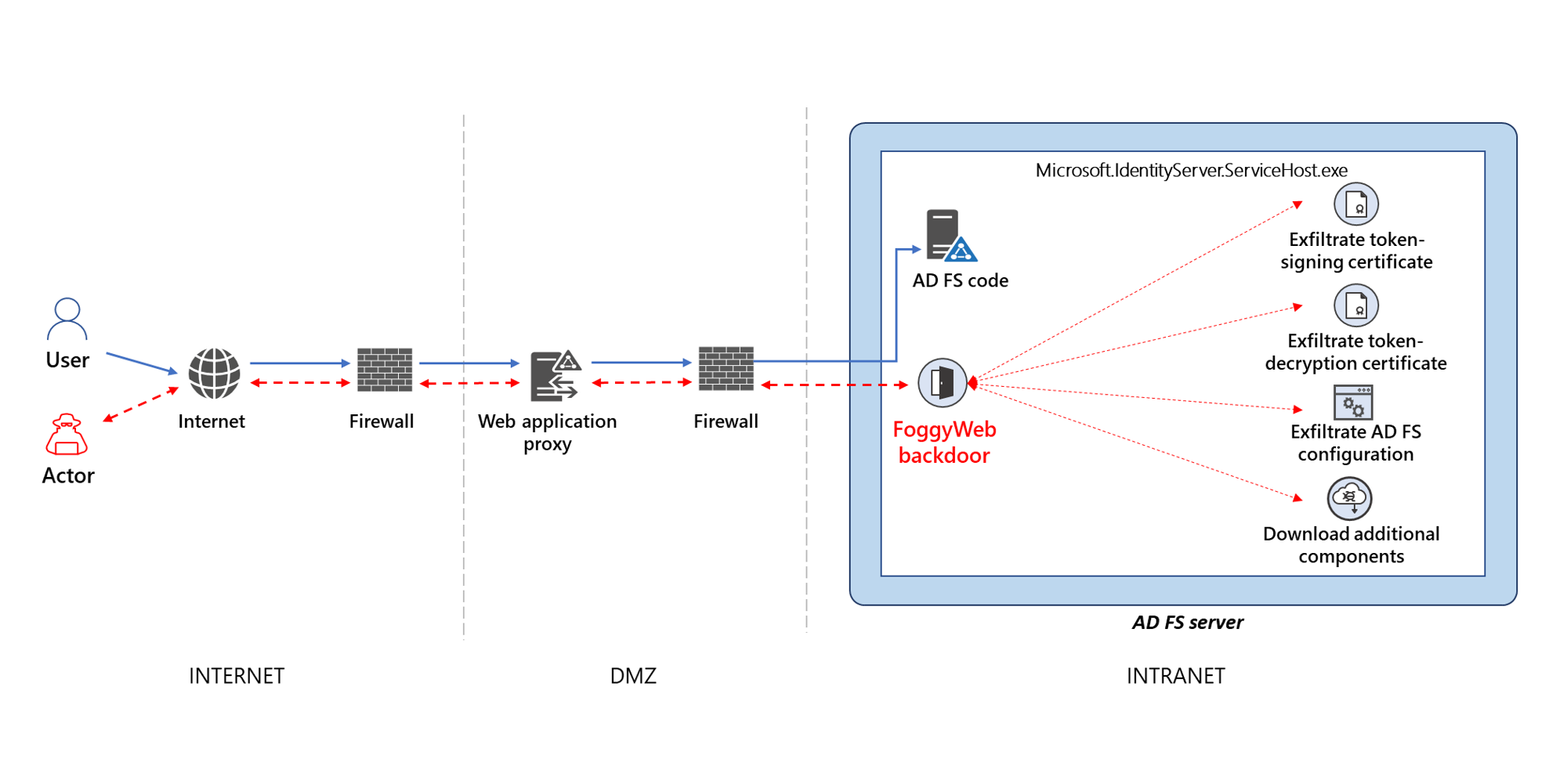
21 - https://www.microsoft.com/security/blog/2021/09/27/foggyweb-targeted-nobelium-malware-leads-to-persistent-backdoor/
22author: Nasreddine Bencherchali (Nextron Systems)
23date: 2023-03-31
24modified: 2024-11-23
25tags:
26 - attack.defense-evasion
27 - detection.emerging-threats
28logsource:
29 category: image_load
30 product: windows
31detection:
32 selection:
33 Hashes|contains:
34 # ffmpeg.dll
35 - 'SHA256=7986BBAEE8940DA11CE089383521AB420C443AB7B15ED42AED91FD31CE833896'
36 - 'SHA1=BF939C9C261D27EE7BB92325CC588624FCA75429'
37 - 'MD5=74BC2D0B6680FAA1A5A76B27E5479CBC'
38 # d3dcompiler_47.dll
39 - 'SHA256=11BE1803E2E307B647A8A7E02D128335C448FF741BF06BF52B332E0BBF423B03'
40 - 'SHA1=20D554A80D759C50D6537DD7097FED84DD258B3E'
41 - 'MD5=82187AD3F0C6C225E2FBA0C867280CC9'
42 # Inner object from ffmpeg.dll
43 - 'SHA256=F79C3B0ADB6EC7BCC8BC9AE955A1571AAED6755A28C8B17B1D7595EE86840952'
44 - 'SHA1=894E7D4FFD764BB458809C7F0643694B036EAD30'
45 - 'MD5=11BC82A9BD8297BD0823BCE5D6202082'
46 # ICONIC Stealer payload
47 - 'SHA256=8AB3A5EAAF8C296080FADF56B265194681D7DA5DA7C02562953A4CB60E147423'
48 - 'SHA1=3B3E778B647371262120A523EB873C20BB82BEAF'
49 - 'MD5=7FAEA2B01796B80D180399040BB69835'
50 condition: selection
51falsepositives:
52 - Unlikely
53level: critical
References
Related rules
- Potential Compromised 3CXDesktopApp Execution
- Diamond Sleet APT Scheduled Task Creation - Registry
- APT PRIVATELOG Image Load Pattern
- APT29 2018 Phishing Campaign CommandLine Indicators
- APT29 2018 Phishing Campaign File Indicators