OWASSRF Exploitation Attempt Using Public POC - Proxy
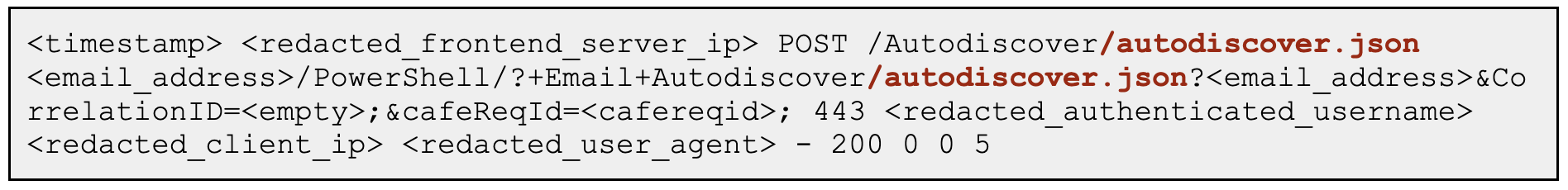
Detects exploitation attempt of the OWASSRF variant targeting exchange servers using publicly available POC. It uses the OWA endpoint to access the powershell backend endpoint
Sigma rule (View on GitHub)
1title: OWASSRF Exploitation Attempt Using Public POC - Proxy
2id: fdd7e904-7304-4616-a46a-e32f917c4be4
3status: test
4description: Detects exploitation attempt of the OWASSRF variant targeting exchange servers using publicly available POC. It uses the OWA endpoint to access the powershell backend endpoint
5references:
6 - https://www.crowdstrike.com/blog/owassrf-exploit-analysis-and-recommendations/
7 - https://www.rapid7.com/blog/post/2022/12/21/cve-2022-41080-cve-2022-41082-rapid7-observed-exploitation-of-owassrf-in-exchange-for-rce/
8 - https://twitter.com/purp1ew0lf/status/1602989967776808961?s=12&t=OkZJl_ViICeiftVEsohRyw
9author: Nasreddine Bencherchali (Nextron Systems)
10date: 2022-12-22
11tags:
12 - attack.initial-access
13 - attack.t1190
14 - detection.emerging-threats
15logsource:
16 category: proxy
17detection:
18 selection:
19 # Look for the header: X-OWA-ExplicitLogonUser: owa/mastermailbox@outlook.com
20 c-useragent: 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/105.0.5195.54 Safari/537.36'
21 cs-method: 'POST'
22 sc-status: 200
23 c-uri|contains|all:
24 - '/owa/mastermailbox'
25 - '/powershell'
26 condition: selection
27falsepositives:
28 - Unlikely
29level: critical
References
Related rules
- CVE-2023-22518 Exploitation Attempt - Suspicious Confluence Child Process (Linux)
- CVE-2023-22518 Exploitation Attempt - Suspicious Confluence Child Process (Windows)
- CVE-2023-22518 Exploitation Attempt - Vulnerable Endpoint Connection (Proxy)
- CVE-2023-22518 Exploitation Attempt - Vulnerable Endpoint Connection (Webserver)
- CVE-2023-46747 Exploitation Activity - Proxy