AdFind Command Activity
This rule detects the Active Directory query tool, AdFind.exe. AdFind has legitimate purposes, but it is frequently leveraged by threat actors to perform post-exploitation Active Directory reconnaissance. The AdFind tool has been observed in Trickbot, Ryuk, Maze, and FIN6 campaigns. For Winlogbeat, this rule requires Sysmon.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2020/10/19"
3integration = ["endpoint", "windows", "system", "m365_defender", "sentinel_one_cloud_funnel", "crowdstrike"]
4maturity = "production"
5updated_date = "2025/03/20"
6
7[rule]
8author = ["Elastic"]
9description = """
10This rule detects the Active Directory query tool, AdFind.exe. AdFind has legitimate purposes, but it is frequently
11leveraged by threat actors to perform post-exploitation Active Directory reconnaissance. The AdFind tool has been
12observed in Trickbot, Ryuk, Maze, and FIN6 campaigns. For Winlogbeat, this rule requires Sysmon.
13"""
14from = "now-9m"
15index = [
16 "endgame-*",
17 "logs-crowdstrike.fdr*",
18 "logs-endpoint.events.process-*",
19 "logs-m365_defender.event-*",
20 "logs-sentinel_one_cloud_funnel.*",
21 "logs-system.security*",
22 "logs-windows.forwarded*",
23 "logs-windows.sysmon_operational-*",
24 "winlogbeat-*",
25]
26language = "eql"
27license = "Elastic License v2"
28name = "AdFind Command Activity"
29note = """## Triage and analysis
30
31### Investigating AdFind Command Activity
32
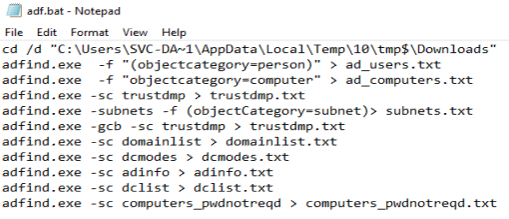
33[AdFind](http://www.joeware.net/freetools/tools/adfind/) is a freely available command-line tool used to retrieve information from Active Directory (AD). Network discovery and enumeration tools like `AdFind` are useful to adversaries in the same ways they are effective for network administrators. This tool provides quick ability to scope AD person/computer objects and understand subnets and domain information. There are many [examples](https://thedfirreport.com/category/adfind/) of this tool being adopted by ransomware and criminal groups and used in compromises.
34
35#### Possible investigation steps
36
37- Investigate the process execution chain (parent process tree) for unknown processes. Examine their executable files for prevalence, whether they are located in expected locations, and if they are signed with valid digital signatures.
38- Identify the user account that performed the action and whether it should perform this kind of action.
39- Examine the command line to determine what information was retrieved by the tool.
40- Contact the account owner and confirm whether they are aware of this activity.
41- Investigate other alerts associated with the user/host during the past 48 hours.
42
43### False positive analysis
44
45- This rule has a high chance to produce false positives as it is a legitimate tool used by network administrators.
46- If this rule is noisy in your environment due to expected activity, consider adding exceptions — preferably with a combination of user and command line conditions.
47- Malicious behavior with `AdFind` should be investigated as part of a step within an attack chain. It doesn't happen in isolation, so reviewing previous logs/activity from impacted machines can be very telling.
48
49### Related rules
50
51- Windows Network Enumeration - 7b8bfc26-81d2-435e-965c-d722ee397ef1
52- Enumeration of Administrator Accounts - 871ea072-1b71-4def-b016-6278b505138d
53- Enumeration Command Spawned via WMIPrvSE - 770e0c4d-b998-41e5-a62e-c7901fd7f470
54
55### Response and remediation
56
57- Initiate the incident response process based on the outcome of the triage.
58- Isolate the involved host to prevent further post-compromise behavior.
59- Investigate credential exposure on systems compromised or used by the attacker to ensure all compromised accounts are identified. Reset passwords for these accounts and other potentially compromised credentials, such as email, business systems, and web services.
60- Run a full antimalware scan. This may reveal additional artifacts left in the system, persistence mechanisms, and malware components.
61- Determine the initial vector abused by the attacker and take action to prevent reinfection through the same vector.
62- Using the incident response data, update logging and audit policies to improve the mean time to detect (MTTD) and the mean time to respond (MTTR).
63"""
64references = [
65 "http://www.joeware.net/freetools/tools/adfind/",
66 "https://thedfirreport.com/2020/05/08/adfind-recon/",
67 "https://www.fireeye.com/blog/threat-research/2020/05/tactics-techniques-procedures-associated-with-maze-ransomware-incidents.html",
68 "https://www.cybereason.com/blog/dropping-anchor-from-a-trickbot-infection-to-the-discovery-of-the-anchor-malware",
69 "https://www.fireeye.com/blog/threat-research/2019/04/pick-six-intercepting-a-fin6-intrusion.html",
70 "https://usa.visa.com/dam/VCOM/global/support-legal/documents/fin6-cybercrime-group-expands-threat-To-ecommerce-merchants.pdf",
71]
72risk_score = 21
73rule_id = "eda499b8-a073-4e35-9733-22ec71f57f3a"
74severity = "low"
75tags = [
76 "Domain: Endpoint",
77 "OS: Windows",
78 "Use Case: Threat Detection",
79 "Tactic: Discovery",
80 "Resources: Investigation Guide",
81 "Data Source: Elastic Endgame",
82 "Data Source: Elastic Defend",
83 "Data Source: Windows Security Event Logs",
84 "Data Source: Microsoft Defender for Endpoint",
85 "Data Source: Sysmon",
86 "Data Source: SentinelOne",
87 "Data Source: Crowdstrike",
88]
89timestamp_override = "event.ingested"
90type = "eql"
91
92query = '''
93process where host.os.type == "windows" and event.type == "start" and
94 (process.name : "AdFind*.exe" or ?process.pe.original_file_name == "AdFind.exe") and
95 process.args : ("objectcategory=computer", "(objectcategory=computer)",
96 "objectcategory=person", "(objectcategory=person)",
97 "objectcategory=subnet", "(objectcategory=subnet)",
98 "objectcategory=group", "(objectcategory=group)",
99 "objectcategory=organizationalunit", "(objectcategory=organizationalunit)",
100 "objectcategory=attributeschema", "(objectcategory=attributeschema)",
101 "domainlist", "dcmodes", "adinfo", "dclist", "computers_pwnotreqd", "trustdmp")
102'''
103
104
105[[rule.threat]]
106framework = "MITRE ATT&CK"
107[[rule.threat.technique]]
108id = "T1016"
109name = "System Network Configuration Discovery"
110reference = "https://attack.mitre.org/techniques/T1016/"
111
112[[rule.threat.technique]]
113id = "T1018"
114name = "Remote System Discovery"
115reference = "https://attack.mitre.org/techniques/T1018/"
116
117[[rule.threat.technique]]
118id = "T1069"
119name = "Permission Groups Discovery"
120reference = "https://attack.mitre.org/techniques/T1069/"
121[[rule.threat.technique.subtechnique]]
122id = "T1069.002"
123name = "Domain Groups"
124reference = "https://attack.mitre.org/techniques/T1069/002/"
125
126
127[[rule.threat.technique]]
128id = "T1087"
129name = "Account Discovery"
130reference = "https://attack.mitre.org/techniques/T1087/"
131[[rule.threat.technique.subtechnique]]
132id = "T1087.002"
133name = "Domain Account"
134reference = "https://attack.mitre.org/techniques/T1087/002/"
135
136
137[[rule.threat.technique]]
138id = "T1482"
139name = "Domain Trust Discovery"
140reference = "https://attack.mitre.org/techniques/T1482/"
141
142
143[rule.threat.tactic]
144id = "TA0007"
145name = "Discovery"
146reference = "https://attack.mitre.org/tactics/TA0007/"
Triage and analysis
Investigating AdFind Command Activity
AdFind is a freely available command-line tool used to retrieve information from Active Directory (AD). Network discovery and enumeration tools like AdFind are useful to adversaries in the same ways they are effective for network administrators. This tool provides quick ability to scope AD person/computer objects and understand subnets and domain information. There are many examples of this tool being adopted by ransomware and criminal groups and used in compromises.
Possible investigation steps
- Investigate the process execution chain (parent process tree) for unknown processes. Examine their executable files for prevalence, whether they are located in expected locations, and if they are signed with valid digital signatures.
- Identify the user account that performed the action and whether it should perform this kind of action.
- Examine the command line to determine what information was retrieved by the tool.
- Contact the account owner and confirm whether they are aware of this activity.
- Investigate other alerts associated with the user/host during the past 48 hours.
False positive analysis
- This rule has a high chance to produce false positives as it is a legitimate tool used by network administrators.
- If this rule is noisy in your environment due to expected activity, consider adding exceptions — preferably with a combination of user and command line conditions.
- Malicious behavior with
AdFindshould be investigated as part of a step within an attack chain. It doesn't happen in isolation, so reviewing previous logs/activity from impacted machines can be very telling.
Related rules
- Windows Network Enumeration - 7b8bfc26-81d2-435e-965c-d722ee397ef1
- Enumeration of Administrator Accounts - 871ea072-1b71-4def-b016-6278b505138d
- Enumeration Command Spawned via WMIPrvSE - 770e0c4d-b998-41e5-a62e-c7901fd7f470
Response and remediation
- Initiate the incident response process based on the outcome of the triage.
- Isolate the involved host to prevent further post-compromise behavior.
- Investigate credential exposure on systems compromised or used by the attacker to ensure all compromised accounts are identified. Reset passwords for these accounts and other potentially compromised credentials, such as email, business systems, and web services.
- Run a full antimalware scan. This may reveal additional artifacts left in the system, persistence mechanisms, and malware components.
- Determine the initial vector abused by the attacker and take action to prevent reinfection through the same vector.
- Using the incident response data, update logging and audit policies to improve the mean time to detect (MTTD) and the mean time to respond (MTTR).
References
Related rules
- Enumerating Domain Trusts via DSQUERY.EXE
- Group Policy Discovery via Microsoft GPResult Utility
- Peripheral Device Discovery
- Wireless Credential Dumping using Netsh Command
- Code Signing Policy Modification Through Built-in tools