Suspicious Execution from a Mounted Device
Identifies when a script interpreter or signed binary is launched via a non-standard working directory. An attacker may use this technique to evade defenses.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2021/05/28"
3integration = ["endpoint", "windows"]
4maturity = "production"
5updated_date = "2026/02/23"
6
7[rule]
8author = ["Elastic"]
9description = """
10Identifies when a script interpreter or signed binary is launched via a non-standard working directory. An attacker may
11use this technique to evade defenses.
12"""
13from = "now-9m"
14index = ["winlogbeat-*", "logs-endpoint.events.process-*", "logs-windows.sysmon_operational-*"]
15language = "eql"
16license = "Elastic License v2"
17name = "Suspicious Execution from a Mounted Device"
18note = """## Triage and analysis
19
20> **Disclaimer**:
21> This investigation guide was created using generative AI technology and has been reviewed to improve its accuracy and relevance. While every effort has been made to ensure its quality, we recommend validating the content and adapting it to suit your specific environment and operational needs.
22
23### Investigating Suspicious Execution from a Mounted Device
24
25In Windows environments, script interpreters and signed binaries are essential for executing legitimate tasks. However, adversaries can exploit these by launching them from non-standard directories, such as mounted devices, to bypass security measures. The detection rule identifies such anomalies by monitoring processes initiated from unexpected directories, especially when triggered by common parent processes like explorer.exe, thus flagging potential defense evasion attempts.
26
27### Possible investigation steps
28
29- Review the process details to confirm the executable path and working directory, ensuring they match the criteria of being launched from a non-standard directory (e.g., not from "C:\\\\").
30- Investigate the parent process, explorer.exe, to determine if there are any unusual activities or user actions that might have triggered the suspicious execution.
31- Check the user account associated with the process to verify if the activity aligns with their typical behavior or if the account might be compromised.
32- Analyze the command line arguments used by the suspicious process to identify any potentially malicious scripts or commands being executed.
33- Correlate the event with other security alerts or logs from the same host to identify any patterns or additional indicators of compromise.
34- Examine the mounted device from which the process was executed to determine its origin, legitimacy, and any associated files that might be malicious.
35
36### False positive analysis
37
38- Legitimate software installations or updates may trigger the rule if they are executed from a mounted device. Users can create exceptions for known software update processes that are verified as safe.
39- Portable applications running from USB drives or external storage can be flagged. To mitigate this, users should whitelist specific applications that are frequently used and deemed non-threatening.
40- IT administrative scripts executed from network shares or mounted drives for maintenance tasks might be detected. Users can exclude these scripts by specifying trusted network paths or script names.
41- Development environments where scripts are tested from non-standard directories can cause alerts. Developers should ensure their working directories are recognized as safe or use designated development machines with adjusted monitoring rules.
42- Backup or recovery operations that utilize mounted devices for script execution may be misidentified. Users should identify and exclude these operations by defining exceptions for known backup tools and processes.
43
44### Response and remediation
45
46- Isolate the affected system from the network to prevent further malicious activity and lateral movement.
47- Terminate any suspicious processes identified by the detection rule, such as those initiated by script interpreters or signed binaries from non-standard directories.
48- Conduct a forensic analysis of the mounted device and the affected system to identify any malicious payloads or scripts and remove them.
49- Review and restore any altered system configurations or registry settings to their original state to ensure system integrity.
50- Update and patch the system to close any vulnerabilities that may have been exploited by the attacker.
51- Monitor for any recurrence of similar activities by enhancing logging and alerting mechanisms, focusing on process execution from non-standard directories.
52- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to determine if additional systems are affected."""
53references = [
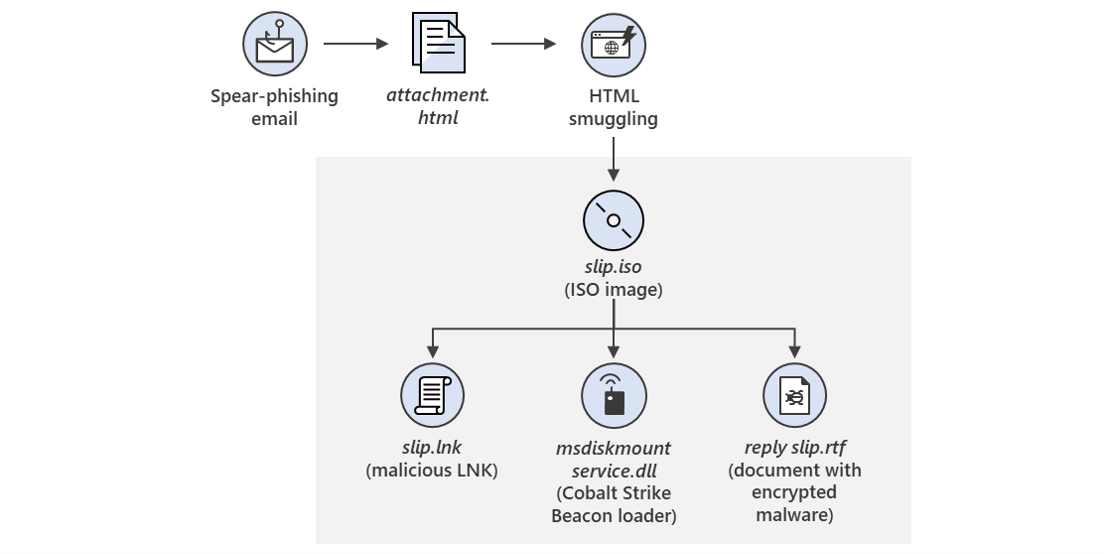
54 "https://www.microsoft.com/security/blog/2021/05/27/new-sophisticated-email-based-attack-from-nobelium/",
55 "https://www.volexity.com/blog/2021/05/27/suspected-apt29-operation-launches-election-fraud-themed-phishing-campaigns/",
56]
57risk_score = 47
58rule_id = "8a1d4831-3ce6-4859-9891-28931fa6101d"
59severity = "medium"
60tags = [
61 "Domain: Endpoint",
62 "OS: Windows",
63 "Use Case: Threat Detection",
64 "Tactic: Defense Evasion",
65 "Tactic: Execution",
66 "Data Source: Elastic Defend",
67 "Data Source: Sysmon",
68 "Resources: Investigation Guide",
69]
70timestamp_override = "event.ingested"
71type = "eql"
72
73query = '''
74process where host.os.type == "windows" and event.type == "start" and process.executable : "C:\\*" and
75 (
76 process.working_directory : ("D:\\*", "E:\\*", "F:\\*") or
77 ?process.Ext.device.product_id : ("Virtual DVD-ROM", "Virtual Disk")
78 ) and
79 process.parent.name : "explorer.exe" and
80 process.name : (
81 "rundll32.exe", "mshta.exe", "powershell.exe", "pwsh.exe", "cmd.exe", "regsvr32.exe", "cscript.exe",
82 "wscript.exe", "certutil.exe", "bitsadmin.exe", "msiexec.exe", "wmic.exe", "schtasks.exe", "msbuild.exe"
83 )
84'''
85
86
87[[rule.threat]]
88framework = "MITRE ATT&CK"
89[[rule.threat.technique]]
90id = "T1218"
91name = "System Binary Proxy Execution"
92reference = "https://attack.mitre.org/techniques/T1218/"
93[[rule.threat.technique.subtechnique]]
94id = "T1218.005"
95name = "Mshta"
96reference = "https://attack.mitre.org/techniques/T1218/005/"
97
98[[rule.threat.technique.subtechnique]]
99id = "T1218.010"
100name = "Regsvr32"
101reference = "https://attack.mitre.org/techniques/T1218/010/"
102
103[[rule.threat.technique.subtechnique]]
104id = "T1218.011"
105name = "Rundll32"
106reference = "https://attack.mitre.org/techniques/T1218/011/"
107
108
109
110[rule.threat.tactic]
111id = "TA0005"
112name = "Defense Evasion"
113reference = "https://attack.mitre.org/tactics/TA0005/"
114[[rule.threat]]
115framework = "MITRE ATT&CK"
116[[rule.threat.technique]]
117id = "T1059"
118name = "Command and Scripting Interpreter"
119reference = "https://attack.mitre.org/techniques/T1059/"
120[[rule.threat.technique.subtechnique]]
121id = "T1059.001"
122name = "PowerShell"
123reference = "https://attack.mitre.org/techniques/T1059/001/"
124
125[[rule.threat.technique.subtechnique]]
126id = "T1059.003"
127name = "Windows Command Shell"
128reference = "https://attack.mitre.org/techniques/T1059/003/"
129
130
131
132[rule.threat.tactic]
133id = "TA0002"
134name = "Execution"
135reference = "https://attack.mitre.org/tactics/TA0002/"
Triage and analysis
Disclaimer: This investigation guide was created using generative AI technology and has been reviewed to improve its accuracy and relevance. While every effort has been made to ensure its quality, we recommend validating the content and adapting it to suit your specific environment and operational needs.
Investigating Suspicious Execution from a Mounted Device
In Windows environments, script interpreters and signed binaries are essential for executing legitimate tasks. However, adversaries can exploit these by launching them from non-standard directories, such as mounted devices, to bypass security measures. The detection rule identifies such anomalies by monitoring processes initiated from unexpected directories, especially when triggered by common parent processes like explorer.exe, thus flagging potential defense evasion attempts.
Possible investigation steps
- Review the process details to confirm the executable path and working directory, ensuring they match the criteria of being launched from a non-standard directory (e.g., not from "C:\").
- Investigate the parent process, explorer.exe, to determine if there are any unusual activities or user actions that might have triggered the suspicious execution.
- Check the user account associated with the process to verify if the activity aligns with their typical behavior or if the account might be compromised.
- Analyze the command line arguments used by the suspicious process to identify any potentially malicious scripts or commands being executed.
- Correlate the event with other security alerts or logs from the same host to identify any patterns or additional indicators of compromise.
- Examine the mounted device from which the process was executed to determine its origin, legitimacy, and any associated files that might be malicious.
False positive analysis
- Legitimate software installations or updates may trigger the rule if they are executed from a mounted device. Users can create exceptions for known software update processes that are verified as safe.
- Portable applications running from USB drives or external storage can be flagged. To mitigate this, users should whitelist specific applications that are frequently used and deemed non-threatening.
- IT administrative scripts executed from network shares or mounted drives for maintenance tasks might be detected. Users can exclude these scripts by specifying trusted network paths or script names.
- Development environments where scripts are tested from non-standard directories can cause alerts. Developers should ensure their working directories are recognized as safe or use designated development machines with adjusted monitoring rules.
- Backup or recovery operations that utilize mounted devices for script execution may be misidentified. Users should identify and exclude these operations by defining exceptions for known backup tools and processes.
Response and remediation
- Isolate the affected system from the network to prevent further malicious activity and lateral movement.
- Terminate any suspicious processes identified by the detection rule, such as those initiated by script interpreters or signed binaries from non-standard directories.
- Conduct a forensic analysis of the mounted device and the affected system to identify any malicious payloads or scripts and remove them.
- Review and restore any altered system configurations or registry settings to their original state to ensure system integrity.
- Update and patch the system to close any vulnerabilities that may have been exploited by the attacker.
- Monitor for any recurrence of similar activities by enhancing logging and alerting mechanisms, focusing on process execution from non-standard directories.
- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to determine if additional systems are affected.
References
Related rules
- Clearing Windows Console History
- Microsoft Build Engine Started an Unusual Process
- Microsoft Build Engine Started by a Script Process
- GenAI Process Compiling or Generating Executables
- Disabling Windows Defender Security Settings via PowerShell