Potential REMCOS Trojan Execution
Identifies known execution traces of the REMCOS Remote Access Trojan. Remcos RAT is used by attackers to perform actions on infected machines remotely.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2025/08/20"
3integration = ["endpoint", "windows", "sentinel_one_cloud_funnel", "m365_defender", "system"]
4maturity = "production"
5updated_date = "2025/08/20"
6
7[rule]
8author = ["Elastic"]
9description = """
10Identifies known execution traces of the REMCOS Remote Access Trojan. Remcos RAT is used by attackers to perform actions on infected machines remotely.
11"""
12from = "now-9m"
13index = [
14 "endgame-*",
15 "logs-endpoint.events.registry-*",
16 "logs-endpoint.events.file-*",
17 "logs-m365_defender.event-*",
18 "logs-sentinel_one_cloud_funnel.*",
19 "logs-system.security*",
20 "logs-windows.sysmon_operational-*",
21 "winlogbeat-*",
22]
23language = "eql"
24license = "Elastic License v2"
25name = "Potential REMCOS Trojan Execution"
26note = """## Triage and analysis
27
28### Investigating Potential REMCOS Trojan Execution
29
30Remcos RAT is used by attackers to perform actions on infected machines remotely.
31
32### Possible investigation steps
33
34- Review the origin of the REMCOS file and the execution chain to identify the initial vector..
35- Examine if the process is set to persist in the affected system via scheduled task, Startup folder or Run key.
36- Check the network, files and child processes activity associated with the every suspicious process in the execution chain of REMCOS.
37- Correlate the event with other security alerts or logs from data sources like Elastic Defend or Microsoft Defender for Endpoint to gather additional context and identify any related malicious activities.
38
39### Response and remediation
40
41- Immediately isolate the affected system from the network to prevent further unauthorized access or lateral movement by the attacker.
42- Terminate any suspicious processes identified in the alert, such as PowerShell, cmd.exe, or other flagged executables, to halt any ongoing malicious activity.
43- Review and revoke any unauthorized user accounts or privileges that may have been created or modified using tools like net.exe or schtasks.exe.
44- Conduct a thorough scan of the affected system using endpoint protection tools to identify and remove any malware or unauthorized software installed by the attacker.
45- Restore the system from a known good backup if any critical system files or configurations have been altered or compromised.
46- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to determine if additional systems are affected.
47- Implement enhanced monitoring and logging for ScreenConnect and other remote access tools to detect similar activities in the future, ensuring that alerts are promptly reviewed and acted upon."""
48references = [
49 "https://any.run/malware-trends/remcos",
50 "https://attack.mitre.org/software/S0332/",
51 "https://www.elastic.co/security-labs/exploring-the-ref2731-intrusion-set"
52]
53risk_score = 73
54rule_id = "d8b2f85a-cf1c-40fc-acf0-bb5d588a8ea6"
55severity = "high"
56tags = [
57 "Domain: Endpoint",
58 "OS: Windows",
59 "Use Case: Threat Detection",
60 "Tactic: Command and Control",
61 "Resources: Investigation Guide",
62 "Data Source: Elastic Endgame",
63 "Data Source: Elastic Defend",
64 "Data Source: Sysmon",
65 "Data Source: SentinelOne",
66 "Data Source: Microsoft Defender for Endpoint",
67 "Data Source: Windows Security Event Logs"
68]
69timestamp_override = "event.ingested"
70type = "eql"
71
72query = '''
73any where host.os.type == "windows" and
74(
75 (event.category == "file" and event.type == "deletion" and file.path like "C:\\Users\\*\\AppData\\Local\\Temp\\TH????.tmp") or
76
77 (event.category == "file" and file.path : "?:\\Users\\*\\AppData\\Roaming\\remcos\\logs.dat") or
78
79 (event.category == "registry" and
80 registry.value : ("Remcos", "Rmc-??????", "licence") and
81 registry.path : (
82 "*\\Windows\\CurrentVersion\\Run\\Remcos",
83 "*\\Windows\\CurrentVersion\\Run\\Rmc-??????",
84 "*\\SOFTWARE\\Remcos-*\\licence",
85 "*\\Software\\Rmc-??????\\licence"
86 )
87 )
88)
89'''
90
91
92[[rule.threat]]
93framework = "MITRE ATT&CK"
94[[rule.threat.technique]]
95id = "T1219"
96name = "Remote Access Tools"
97reference = "https://attack.mitre.org/techniques/T1219/"
98
99
100[rule.threat.tactic]
101id = "TA0011"
102name = "Command and Control"
103reference = "https://attack.mitre.org/tactics/TA0011/"
Triage and analysis
Investigating Potential REMCOS Trojan Execution
Remcos RAT is used by attackers to perform actions on infected machines remotely.
Possible investigation steps
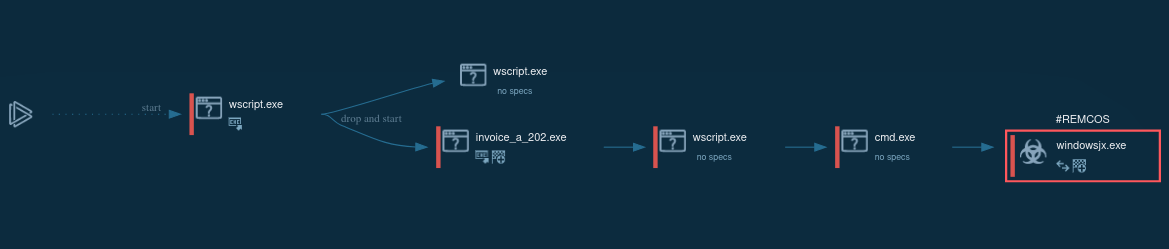
- Review the origin of the REMCOS file and the execution chain to identify the initial vector..
- Examine if the process is set to persist in the affected system via scheduled task, Startup folder or Run key.
- Check the network, files and child processes activity associated with the every suspicious process in the execution chain of REMCOS.
- Correlate the event with other security alerts or logs from data sources like Elastic Defend or Microsoft Defender for Endpoint to gather additional context and identify any related malicious activities.
Response and remediation
- Immediately isolate the affected system from the network to prevent further unauthorized access or lateral movement by the attacker.
- Terminate any suspicious processes identified in the alert, such as PowerShell, cmd.exe, or other flagged executables, to halt any ongoing malicious activity.
- Review and revoke any unauthorized user accounts or privileges that may have been created or modified using tools like net.exe or schtasks.exe.
- Conduct a thorough scan of the affected system using endpoint protection tools to identify and remove any malware or unauthorized software installed by the attacker.
- Restore the system from a known good backup if any critical system files or configurations have been altered or compromised.
- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to determine if additional systems are affected.
- Implement enhanced monitoring and logging for ScreenConnect and other remote access tools to detect similar activities in the future, ensuring that alerts are promptly reviewed and acted upon.
References
Related rules
- NetSupport Manager Execution from an Unusual Path
- Potential File Transfer via Curl for Windows
- Suspicious ScreenConnect Client Child Process
- Potential DNS Tunneling via NsLookup
- Potential File Transfer via Certreq