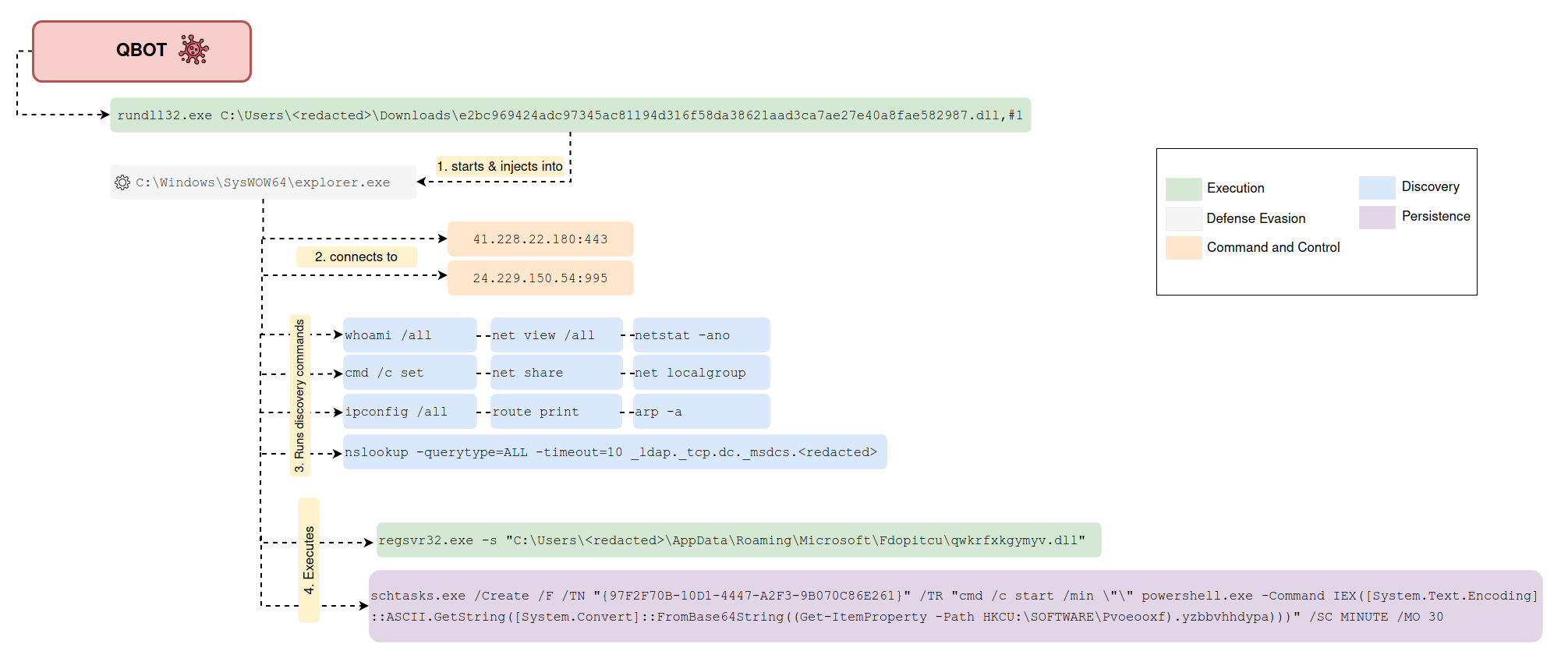
Scheduled task executing powershell encoded payload from registry
Detects the creation of a schtask that executes a base64 encoded payload stored in the Windows Registry using PowerShell.
Sigma rule (View on GitHub)
1title: Scheduled task executing powershell encoded payload from registry
2id: 16e0c76d-dbe9-461b-afce-ced21d819b29
3status: experimental
4description: Detects the creation of a schtask that executes a base64 encoded payload stored in the Windows Registry using PowerShell.
5author: 'Kostastsale, TheDFIRReport'
6references:
7 - https://thedfirreport.com/2022/02/21/qbot-and-zerologon-lead-to-full-domain-compromise/
8date: 2022/02/12
9modified: 2023/01/08
10logsource:
11 product: windows
12 category: process_creation
13detection:
14 selection1:
15 Image|endswith: '\schtasks.exe'
16 CommandLine|contains|all:
17 - '/Create'
18 - '/SC'
19 selection2:
20 CommandLine|contains|all:
21 - 'FromBase64String'
22 - 'powershell'
23 - 'Get-ItemProperty'
24 - 'HKCU:'
25 condition: selection1 and selection2
26falsepositives:
27 - Unknown
28level: medium
29tags:
30 - attack.execution
31 - attack.persistence
32 - attack.t1053.005
33 - attack.t1059.001
References
Related rules
- Scheduled task executing powershell encoded payload from registry
- PowerShell Create Local User
- Windows Scheduled Task Behaving Improperly or Suspiciously
- Windows Scheduled Task Create Shell
- Windows Scheduled Task Making Suspicious Network Connection